A significant security vulnerability was uncovered in the AWS Cloud Development Kit (CDK), an open-source framework widely used by developers to define cloud infrastructure using familiar programming languages.
This vulnerability could allow attackers to gain unauthorized access to S3 buckets, potentially leading to full account takeovers.
The vulnerability was discovered during research that examined over 38,000 well-known AWS account IDs.
It was found that certain AWS CDK users were susceptible due to the manual deletion of their deployment artifact S3 buckets.
National Cybersecurity Awareness Month Cyber Challenges – Test your Skills Now
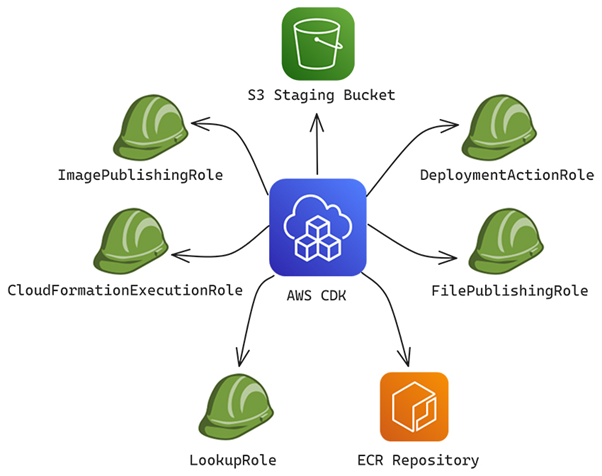
As confirmed by AWS, this issue affected approximately 1% of CDK users. The core problem lies in the predictability of the S3 bucket naming convention during the CDK bootstrapping process.
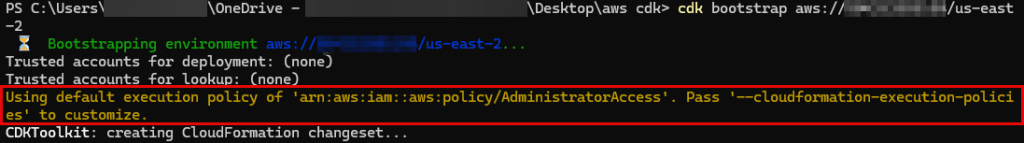
By default, these buckets follow a constant qualifier pattern, making it easier for attackers to anticipate bucket names if they know the target’s AWS Account ID and region.
Exploitation Techniques
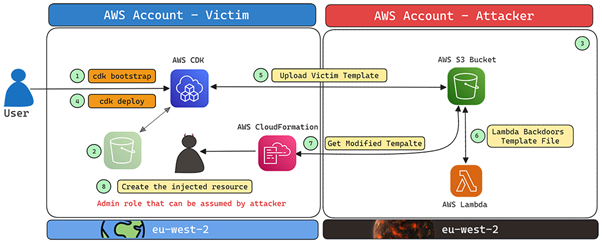
The vulnerability allows for “S3 Bucket Namesquatting” or “Bucket Sniping,” where an attacker can claim a CDK staging S3 bucket before the legitimate user creates it.
If the victim’s CDK writes and reads data from this attacker-controlled bucket, it could lead to severe security implications, including data manipulation and malicious actions within the victim’s AWS account.
In scenarios where users delete their CDK staging S3 bucket after bootstrapping, attackers can exploit this by creating a new bucket with the same predictable name.
When the victim uses CDK again, particularly during a cdk deploy, they might unknowingly interact with this malicious bucket.
According to Aquasec’s discovery, the issue was promptly reported to AWS and swiftly addressed.
AWS released a fix in CDK version v2.149.0, ensuring that assets are only uploaded to buckets within the user’s account.
Additionally, AWS updated its documentation to emphasize customizing bootstrapping resources and using non-default qualifiers.
AWS also directly notified potentially affected customers and added alerts in the CLI terminal to encourage users to upgrade their bootstrap resources.
Users who have employed CDK version v2.148.1 or earlier are advised to upgrade to version v2.149.0 or later and re-run the cdk bootstrap command.
Alternatively, users can apply an IAM policy condition to their FilePublishingRole CDK role to restrict bucket access.
This vulnerability highlights the importance of securing cloud infrastructure and being vigilant about default configurations that could expose systems to attacks.
While AWS has addressed this issue for new users, those previously bootstrapped with older versions must proactively protect their accounts.
The collaboration between researchers and AWS underscores the critical need for continuous monitoring and improvement of cloud security practices.
Free Webinar on How to Protect Small Businesses Against Advanced Cyberthreats -> Watch Here



