The Best SIEM tools for you will depend on your specific requirements, budget, and organizational needs. There are several popular and highly regarded SIEM (Security Information and Event Management) tools available in the market
What is SIEM?
A security information and event management (SIEM) system is the foundation of security processes in the modern security operations center (SOC).
A SIEM saves security analysts the effort of monitoring many different systems.
SIEM systems integrate with security tools, network monitoring tools, performance monitoring tools, critical servers and endpoints, and other IT systems.
It aggregates the data, correlates it, analyzes it to discover anomalous or suspicious activity, and generates alerts when it identifies an activity that might be a security incident.
Every cybersecurity workflow starts from log data collection and management, that’s why we curated the Best SIEM Tools list that is highly demanded among enterprises that strive to maintain a stable security posture and comply with necessary regulations.
This overview briefly looks at the top 5 SIEM vendors for the beginning of 2023, both on-premises and cloud-native depending on the infrastructure.
Find out about their distinctive features to choose the best security solution perfectly tailored to your organization-specific needs.
Table of contents
SIEM Capabilities and Applications
SIEM solutions offer various capabilities that provide visibility into a corporate network of devices and apps.
SIEM provides a centralized location for data collection and aggregation, including dashboards that offer insights into overall security and specific threats.
Threat intelligence
SIEM solutions offer insight into known indicators of compromise (IoC) and attacker tactics, techniques, and procedures (TTP).
The tool uses several threat intelligence feeds, organizing and analyzing information on current and potential threats.
Threat detection
SIEM tools can detect threats in various locations, including emails, applications, cloud resources, endpoints, and external threat intelligence sources.
Most SIEM solutions achieve threat detection by employing user and entity behavior analytics (UEBA).
It helps monitor and detect abnormal behaviors indicating a threat, such as compromised accounts and lateral movement.
Alerting and investigation
After detecting a vulnerability, threat, suspicious behavior, or attack, SIEM tools create and send alerts to the relevant personnel for response and mitigation, supporting incident response operations.
You can customize SIEM alerts to suit user needs and use managed rules to react almost in real-time to critical threats.
Some solutions also offer workflow and case management with automatically created investigation instructions.
Compliance and reporting
SIEM solutions support compliance and alert reporting to help organizations simplify compliance reporting.
This functionality includes data dashboards that help monitor privileged user access and retain and organize event information.
Best SIEM Tools List and Keywords
| SIEM Tools | Key features |
|---|---|
| 1. Splunk | 1. Works in the cloud and on-premises log sources 2. Quick threat detection 3. Enables automated actions 4. Log Collection and Management 5. Threat Detection and Response 6. Compliance Management 7. Cloud Security 8. Threat Intelligence |
| 2. IBM Security QRadar | 1. Supports multiple logging protocols 2. Provides AI-powered investigations 3. Runs intelligent root cause analysis 4. Log Collection and Management 5. Threat Detection and Response 6. Compliance Management 7. Cloud Security 8. Threat Intelligence 9. Machine Learning |
| 3. ArcSight | 1. Distributed correlation 2. Baselining and outlier mechanism 3. Compliance with GDPR 4. Log Collection and Management 5. Threat Detection and Response 6. Compliance Management 7. Cloud Security 8. Data Analytics |
| 4. Microsoft Sentinel | 1. Query performance 2. Iteration speed 3. Azure Security Center playbook 4. Log Collection 5. Data Analytics 6. Security Orchestration, Automation, and Response (SOAR) 7. User and Entity Behavior Analytics (UEBA) 8. Network Security Monitoring |
| 5. Google Chronicle Security | 1. Integration With Virustotal 2. Speed Threat Discovery 3. Low False Positive 4. Backstory 5. Advanced Threat Detection 6. Threat Hunting 7. Security Analytics 8. Scalability |
| 6. OSSIM | 1. Log Collection 2. Event Correlation 3. Threat Intelligence 4. Incident Response 5. Asset Discovery 6. Asset Discovery 7. Compliance Management 8. Open Source 9. Scalability |
| 7. OSSEC | 1. File Integrity Monitoring 2. Intrusion Detection 3. Active Response 4. Real-time Monitoring 5. Host-Based Intrusion Detection 6. Open Source 7. Scalability 8. Customizable Rules |
| 8. Wazuh | 1. Threat Detection 2. Open-Source 3. Dashboards and Reports 4. Log Management 5. Host-Based Intrusion Detection 6. Real-Time Monitoring 7. Threat Detection and Response 8. Compliance Management |
| 9. Apache Metron | 1. Data Ingestion 2. Data Enrichment 3. Machine Learning 4. Advanced Analytics 5. Scalability 6. Real-Time Processing 7. Customizable Rules 8. Visualization 9. Open Source |
| 10. SIEMonster | 1. Advanced Analytics 2. Integration 3. Scalability 4. Open-Source 5. Log Collection and Analysis 6. Real-Time Monitoring 7. Customizable Rules 8. Visualization |
| 11. Prelude SIEM | 1. Extensibility 2. Integration 3. Reporting 4. Log Collection and Analysis 5. Real-Time Monitoring 6. Customizable Rules: 7. Visualization 8. Integration |
| 12. Security Onion | 1. Log Collection and Analysis 2. Real-Time Monitoring 3. Threat Detection and Response 4. Network Security Monitoring 5. Intrusion Detection 6. File Integrity Monitoring 7. Visualization 8. Open Source |
| 13. Suricata | 1. Multi-threaded Packet Processing 2. Protocol Parsing 3. Signature-Based Detection 4. Flow Analysis 5. Open Source 6. Community Support 7. File Extraction and Analysis 8. TLS/SSL Decryption |
Best SIEM Tools List 2024
- Splunk
- IBM Security QRadar
- ArcSight
- Microsoft Sentinel
- Google Chronicle Security
- OSSIM
- OSSEC
- Wazuh
- Apache Metron
- SIEMonster
- Prelude SIEM
- Security Onion
- Suricata
As the world shifts its focus to digital transformation, ensuring that your systems and data are secure has become more critical than ever.
1. Splunk
Splunk is an American tech company that produces SIEM Tools for searching, monitoring, and analyzing machine-generated data via a Web-style interface.
Organizations can choose the most applicable setup depending on their infrastructure with the same capabilities available in the cloud or on-premises.
Splunk Enterprise covers the needs of on-premises SOCs, while Splunk Cloud suits cloud and hybrid architectures. This software is infinitely scalable and effectively deals with big data. Splunk can be installed quickly and is compatible with multiple platforms.
This SIEM can monitor and search vast amounts of data from the organization’s log sources. Next, the information gets indexed and correlated within containers, making it available for search.
It is also possible to automatically generate alerts and reports with a detailed visualization, with the Splunk tool in the Best SIEM Tools List.
Splunk provides improved security operations like customizable dashboards, an asset investigator, statistical analysis, incident review, classification, and investigation.
Features
- Log Collection and Management: Splunk can collect and analyze logs from various sources, including servers, network devices, and applications. It can also normalize and index the data for easy searching and reporting.
- Threat Detection and Response: Splunk can identify security threats by correlating events from different sources and analyzing them in real-time. It can also provide automated response capabilities to prevent further damage.
- Compliance Management: Splunk can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR by providing pre-built compliance reports and dashboards.
- User and Entity Behavior Analytics (UEBA): Splunk can detect anomalous behavior by monitoring user and entity activity across the network. This can help identify potential security incidents before they escalate.
- Security Orchestration, Automation, and Response (SOAR): Splunk can automate security processes and workflows to enable faster response times and reduce the workload on security teams.
- Cloud Security: Splunk can monitor and secure cloud environments, including public, private, and hybrid clouds. It can also integrate with cloud-native security services such as AWS Security Hub and Azure Security Center.
- Threat Intelligence: Splunk can integrate with threat intelligence feeds to provide additional context and visibility into potential threats.
- Machine Learning: Splunk can leverage machine learning algorithms to identify patterns and anomalies in data, helping to detect and respond to security threats more effectively.
Key Characteristics:
- Works both with cloud and on-premises log sources
- Allows quick threat detection
- Enables automated actions, workflows, and event sequencing
- Includes the functionality of an asset investigator, statistical analysis, and incident review
Splunk is packed with a lot of valuable functions. It’s one of the popular SIEM Tools used by startups and large-scale businesses across various industries.
Plus, it delivers customizable dashboards so any SOC team can create one that suits their needs and particular system architecture.
For added efficiency and speed, engineers may use the SOC Prime CCM App for Splunk Cloud and on-premises to continuously stream new detection rules directly into their environment and update the existing ones.
2. IBM Security QRadar
QRadar SIEM is available both on-premises and in cloud environments. SOC teams can connect a network of configured devices, apps, workstations, and servers to collect log data. It also helps to ensure accurate threat detection and run prioritization.
The software ingests and correlates data from endpoints, clouds, networks, and users against the latest threat intel feeds. Advanced security analytics helps to track down threats at every stage of the kill chain.
Features
- Log Collection and Management: QRadar can collect logs from various sources, including servers, network devices, and applications. It can also normalize and enrich the data to provide context and make it easier to search and analyze.
- Threat Detection and Response: QRadar can detect security threats by correlating events from multiple sources and analyzing them in real-time. It uses advanced analytics and machine learning algorithms to identify anomalous behavior and potential threats.
- Network Security Monitoring: QRadar can monitor network traffic and identify suspicious activity, such as port scanning, malware infections, and data exfiltration. It can also detect and respond to network-based attacks such as DDoS.
- Vulnerability Management: QRadar can integrate with vulnerability scanners and provide real-time visibility into vulnerabilities and potential attack vectors. It can also help prioritize and track remediation efforts.
- Compliance Management: QRadar can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports, dashboards, automated log retention, and audit capabilities.
- User and Entity Behavior Analytics (UEBA): QRadar can monitor user and entity activity across the network and detect anomalous behavior. This can help identify potential insider threats and other security incidents.
- Cloud Security: QRadar can monitor and secure cloud environments, including public, private, and hybrid clouds. It can also integrate with cloud-native security services such as AWS Security Hub and Microsoft Azure Security Center.
Prominent Features:
- Supports multiple logging protocols
- Provides AI-powered investigations
- Runs intelligent root cause analysis
- Includes zero-trust model
- Generates reports with visualizations
QRadar delivers a number of useful features that can be further enhanced by integrating other IBM security products. It helps to reduce the manual workload through automation and prioritization.
3. ArcSight
ArcSight Enterprise Security Manager (ESM) is one of the SIEM Tools that scalable solution for collecting, correlating, and reporting on security event information.
It collects data from more than 500 types of log sources. Its scalable data collection framework unlocks visibility across the entire organization’s network.
The aggregation, normalization, and data enrichment enable the performance of advanced security analytics throughout the appliance, software, and cloud environments.
Besides the standard ingestion and interpretation of log data, ArcSight offers threat intelligence, security alerts, compliance reporting, and real-time correlation through intuitive user interface dashboards.
The product is compatible with other security tools from ArcSight such as User Behavior Analytics with the Best SIEM Tools List.
Features
- Log Collection and Management: ArcSight can collect and manage logs from a wide range of sources, including servers, network devices, and applications. It can also normalize and enrich the data to provide context and make it easier to search and analyze.
- Threat Detection and Response: ArcSight can detect security threats by correlating events from multiple sources and analyzing them in real time. It uses advanced analytics and machine learning algorithms to identify potential threats and anomalies.
- Network Security Monitoring: ArcSight can monitor network traffic and identify suspicious activity, such as port scanning, malware infections, and data exfiltration. It can also detect and respond to network-based attacks such as DDoS.
- Compliance Management: ArcSight can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports and dashboards, as well as automated log retention and audit capabilities.
- User and Entity Behavior Analytics (UEBA): ArcSight can monitor user and entity activity across the network and detect anomalous behavior. This can help identify potential insider threats and other security incidents.
- Cloud Security: ArcSight can monitor and secure cloud environments, including public, private, and hybrid clouds. It can also integrate with cloud-native security services such as AWS Security Hub and Microsoft Azure Security Center.
- Data Analytics: ArcSight provides advanced data analytics capabilities that enable organizations to identify and investigate security threats. It can analyze large volumes of data in real time and provide visualizations and dashboards to help security teams understand the threat landscape.
Recent Enhancements to ESM Include:
- Distributed correlation via distributed cluster technology
- Baselining and outlier mechanism notification
- Integration with machine learning algorithms
- Compliance with GDPR
- Default content and customizable rule sets
- Community marketplace support
- Asset, network, user, and vulnerability modeling with geo-location
ArcSight is a highly scalable SIEM solution that is popular among large enterprises and suitable for a wide range of cybersecurity environments. Generally, it provides high-speed performance combined with effective threat blocking.
Overall, the SIEM market stretches far beyond the most popular big players. New startups can find cheaper solutions with more services provided on a subscription basis if they wish to keep a small in-house team.
Moreover, cybersecurity enterprises are looking for highly-scalable solutions that will help overcome the pressure of cost and time caused by cross-tool migrations.
The use of automated content translation engines, like Uncoder.IO, enables converting detection algorithms from the Sigma standard to multiple SIEM language formats on the fly while saving time and costs on cross-tool detection.
4. Microsoft Sentinel

Microsoft Sentinel is the best SIEM tool that enhanced the version of the preexisting on-premises SIEM Microsoft Azure Sentinel which also supports cloud-based functionality.
As a result, the number of available ingested events has grown to over 20 billion daily.
Features
- Log Collection and Management: Microsoft Sentinel can collect logs from a wide range of sources, including servers, network devices, and cloud services. It can also normalize and enrich the data to provide context and make it easier to search and analyze.
- Threat Detection and Response: Microsoft Sentinel can detect security threats by correlating events from multiple sources and analyzing them in real time. It uses advanced analytics and machine learning algorithms to identify potential threats and anomalies.
- Network Security Monitoring: Microsoft Sentinel can monitor network traffic and identify suspicious activity, such as port scanning, malware infections, and data exfiltration. It can also detect and respond to network-based attacks such as DDoS.
- Cloud Security: Microsoft Sentinel is designed to work with cloud environments, including Azure, AWS, and GCP. It can monitor cloud services and applications and provide real-time visibility into potential security threats.
- User and Entity Behavior Analytics (UEBA): Microsoft Sentinel can monitor user and entity activity across the network and detect anomalous behavior. This can help identify potential insider threats and other security incidents.
- Compliance Management: Microsoft Sentinel can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports and dashboards, as well as automated log retention and audit capabilities.
- Data Analytics: Microsoft Sentinel provides advanced data analytics capabilities that enable organizations to identify and investigate security threats. It can analyze large volumes of data in real time and provide visualizations and dashboards to help security teams understand the threat landscape.
New Features Include:
- Query performance has become 12 times faster than in the previous version and up to 100 times faster in some particular cases
- The iteration speed of the features set now executes at a faster rate
- The use of out-of-the-box connectors allows easier data ingestion
- Microsoft provides simplified training and onboarding of security engineers for an easy start with the platform
- The newly implemented Azure Security Center playbook automates over 800 Azure subscriptions and soon is about to include 20,000 additional subscriptions
Overall, Microsoft Sentinel is one of the most powerful and best SIEM Tools that offers high performance and needed agility for all kinds of organizations, from small businesses to large-scale enterprises.
Its powerful capabilities for creating analytics rules, hunting, and incident response with playbook support ensure a high level of automation, often demanded by complex networks.
5. Google Chronicle Security
This security analytics platform is built on Google’s infrastructure which gives this platform an edge over its competitors. Chronicle Security offers a cloud-based elastic container for storing enterprises’ security telemetry.
The data integrity is provided by built-in threat signals along with automation capabilities.
Features
- Backstory: Google Chronicle Security’s Backstory feature allows organizations to store and analyze large amounts of security telemetry data from multiple sources in a single location. It can help identify potential security threats and provide context for investigations.
- Advanced Threat Detection: Google Chronicle Security uses advanced machine learning algorithms to detect potential security threats in real time. It can correlate events from multiple sources and provide insights into the root cause of a security incident.
- Integration with VirusTotal: Google Chronicle Security integrates with VirusTotal to provide additional context and threat intelligence. It can identify potential malware and provide insights into its behavior.
- Threat Hunting: Google Chronicle Security’s Threat Hunting feature allows security teams to proactively search for potential security threats. It can analyze large amounts of data and provide insights into potential threats that other security tools may have missed.
- Security Analytics: Google Chronicle Security provides advanced security analytics capabilities that allow organizations to identify potential security threats and investigate security incidents. It can visualize data in a variety of ways to help security teams understand the threat landscape.
- Scalability: Google Chronicle Security is designed to be scalable and flexible. It can handle large amounts of security telemetry data and can be used in a variety of environments, including on-premises, cloud, and hybrid.
- Automatic Updates: Google Chronicle Security provides automatic updates to ensure that organizations are always using the latest version of the tool. This can help prevent security gaps and ensure that organizations are using the latest threat intelligence.
Some of the Other Services Include:
- The integration of the largest malware database in the world by VirusTotal Enterprise
- The improved speed of threat discovery and investigation (within seconds)
- Reduced rate of false positives and elimination of the triaging for speeding up threat hunting and detection
- Retroactive correlation of log data with backing from threat intelligence sources such as Avast and AVG
- Ingestion of large data sets, as well as indexing, correlating, and analyzing in a matter of seconds
Backed by Google’s core infrastructure, Chronicle Security provides a number of services that work together at maximum speed.
Security event and information management, as well as extensive threat detection and analysis, are available driven by the ability to process petabytes of data on a whim.
Chronicle is also compatible with popular cybersecurity solutions like SOC Prime’s Detection as Code platform for collaborative cyber defense, threat hunting, and discovery that helps security teams address the challenges of building custom use cases while making threat detection easier, faster, and more efficient.
6. OSSIM

Deployment model: on-premise
AlienVault OSSIM is an open-source security solution that provides an intuitive platform for analyzing impending security risks. It provides various tools, including event correlation, vulnerability assessment, behavioral monitoring, and asset discovery.
OSSIM provides a complete SIEM by employing correlation capabilities, native log storage, and various open-source projects, such as FProbe, Nagios, Munin, NFSen/NFDump, OSSEC, OpenVAS, PRADS, Suricata, TCPTrack, Snort.
Features
- Log Collection and Management: OSSIM can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Threat Detection and Response: it uses advanced correlation rules and machine learning algorithms to detect potential security threats in real time. It can provide alerts and notifications when potential threats are identified.
- Network Security Monitoring: OSSIM can monitor network traffic and identify suspicious activity, such as port scanning, malware infections, and data exfiltration. It can also detect and respond to network-based attacks such as DDoS.
- Asset Discovery: OSSIM can identify and map assets within an organization’s network, including servers, endpoints, and applications. This can help organizations understand their attack surface and identify potential vulnerabilities.
- Vulnerability Assessment: it can perform vulnerability scans and identify potential security vulnerabilities within an organization’s network. It can provide insights into the severity of the vulnerability and recommended remediation steps.
- Compliance Management: OSSIM can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports, dashboards, automated log retention, and audit capabilities.
- Open Source: OSSIM is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs. This can include creating custom correlation rules, dashboards, and reports.
- Scalability: OSSIM is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
7. OSSEC

Deployment model: on-premise
Atomic Enterprise OSSEC is a cloud-based solution that offers various security and compliance capabilities.
It helps organizations automate cloud, hybrid, and on-premise security processes. OSSEC is based on an open-source security framework that enables you to monitor and route logs and events to multiple SIEMs.
OSSEC offers intrusion detection, compliance reporting, file integrity monitoring, and policy management. It supports many compliance regulations, including JSIG, HIPAA, GDPR, and PCI DSS.
Additionally, the platform lets you manage rules centrally and sends alerts to notify users about security changes to systems or files.
Features
- Log Collection and Analysis: OSSEC can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Host-Based Intrusion Detection: OSSEC can detect potential security threats at the host level, including file system changes, unauthorized access attempts, and malware infections. It can provide alerts and notifications when potential threats are identified.
- Real-Time Monitoring: OSSEC can monitor system activity in real time and provide immediate notifications of any suspicious activity.
- Compliance Management: OSSEC can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports, dashboards, automated log retention, and audit capabilities.
- Customizable Rules: OSSEC provides a set of pre-built rules for detecting common security threats, but also allows organizations to create their own custom rules based on their specific security needs.
- Open Source: OSSEC is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
- Scalability: OSSEC is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
8. Wazuh
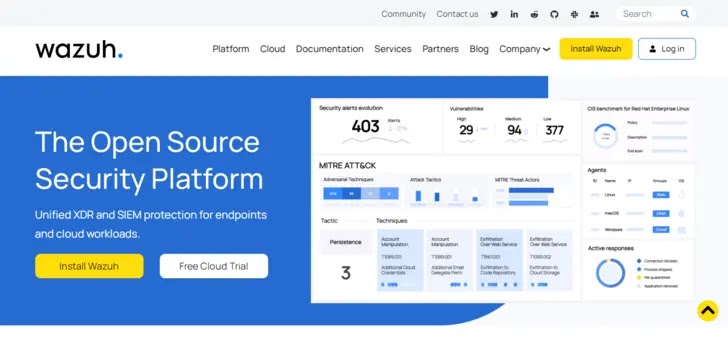
Deployment model: on-premise
Wazuh is an open-source platform that provides threat prevention, detection, and response capabilities. You can use Wazuh to protect workloads across on-premises, containerized, cloud-based, and virtualized environments.
Wazuh employs various mechanisms, including an endpoint security agent that monitors systems. It uses a management server to collect and analyze data collected by these agents.
Additionally, Wazuh is fully integrated with the Elastic Stack, providing a search engine and data visualization tool that enables navigating through security alerts.
Features
- Host-Based Intrusion Detection: Wazuh can detect potential security threats at the host level, including file system changes, unauthorized access attempts, and malware infections. It can provide alerts and notifications when potential threats are identified.
- Log Collection and Analysis: Wazuh can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Real-Time Monitoring: Wazuh can monitor system activity in real time and provide immediate notifications of any suspicious activity.
- Threat Detection and Response: Wazuh uses advanced correlation rules and machine learning algorithms to detect potential security threats in real time. It can provide alerts and notifications when potential threats are identified.
- Compliance Management: Wazuh can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports and dashboards, as well as automated log retention and audit capabilities.
- Customizable Rules: Wazuh provides a set of pre-built rules for detecting common security threats, but also allows organizations to create their own custom rules based on their specific security needs.
- Open Source: Wazuh is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
- Scalability: Wazuh is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
- Integration: Wazuh can integrate with a wide range of other security tools, such as vulnerability scanners, firewalls, and intrusion prevention systems.
9. Apache Metron

Deployment model: on-premise
Apache Metron is a security framework for ingesting, processing, and storing diverse security data feeds at scale. It aims to enable organizations to detect and rapidly respond to cyber anomalies.
Here are the key capabilities of this framework:
- Security data lake or vault—the framework provides cost-effective, long-term storage for enriched telemetry data. You can leverage this data for feature engineering and discovery analytics, as well as search and query operational analytics.
- Pluggable framework—Metron provides a rich set of parsers for common security data sources, including pcap, bro, netflow, snort, sourcefire, and fireye. It also offers a pluggable framework. You can use it to add new custom parsers for various new data sources and add new enrichment services for context. It lets you use pluggable extensions for threat intel feeds and customize your security dashboards.
- Security application—the framework offers standard SIEM capabilities, including alerting, agents to ingest data sources, and threat intel framework. It also includes packet replay utilities and hunting services.
- Threat intelligence—the framework provides next-generation defense techniques that employ anomaly detection and machine learning algorithms in real-time while events stream in.
Features
- Scalability: Apache Metron is designed to handle large amounts of data, making it suitable for organizations of all sizes. It uses a distributed architecture that can be deployed on-premises or in the cloud.
- Data Ingestion: Apache Metron can ingest data from a wide range of sources, including network traffic, system logs, and threat intelligence feeds. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Real-Time Processing: Apache Metron uses real-time processing to detect and respond to security threats as they occur. It can apply machine learning and behavioral analytics to identify anomalies and potential threats.
- Threat Detection and Response: Apache Metron provides a range of tools for detecting and responding to security threats, including correlation rules, threat intelligence, and incident response workflows. It can provide alerts and notifications when potential threats are identified.
- Customizable Rules: Apache Metron provides a set of pre-built rules for detecting common security threats, but also allows organizations to create their own custom rules based on their specific security needs.
- Integration: Apache Metron can integrate with a wide range of other security tools, such as vulnerability scanners, firewalls, and intrusion prevention systems. It also supports integration with popular big data technologies such as Hadoop and Elasticsearch.
- Visualization: Apache Metron provides a range of visualization tools, including dashboards and graphs, to help organizations monitor their security posture and respond to security incidents.
- Open Source: Apache Metron is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
10. SIEMonster
Deployment model: on-premise
SIEMonster is an enterprise-grade SIEM tool that combines several open-source solutions into one centralized platform to provide real-time threat intelligence. Here are key features of SIEMonster
- Human-based behavior—the tool can integrate with behavioral analysis tools to ensure recorded threats are true and minimize false positives.
- Threat intelligence—the tool offers real-time threat intelligence, including open source or commercial feeds, to stop attacks as they occur.
- Deep learning—the tool employs machine learning for analysis and to automatically kill attacks.
Features
- Log Collection and Analysis: SIEMonster can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Real-Time Monitoring: SIEMonster can monitor system activity in real time and provide immediate notifications of any suspicious activity.
- Threat Detection and Response: SIEMonster uses advanced correlation rules and machine learning algorithms to detect potential security threats in real time. It can provide alerts and notifications when potential threats are identified.
- Compliance Management: SIEMonster can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports, dashboards, automated log retention, and audit capabilities.
- Customizable Rules: SIEMonster provides a set of pre-built rules for detecting common security threats, but also allows organizations to create their own custom rules based on their specific security needs.
- Open Source: SIEMonster is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
- Scalability: SIEMonster is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
- Visualization: SIEMonster provides a range of visualization tools, including dashboards and graphs, to help organizations monitor their security posture and respond to security incidents.
- Integration: SIEMonster can integrate with a wide range of other security tools, such as vulnerability scanners, firewalls, and intrusion prevention systems.
11. Prelude SIEM
Deployment model: on-premise
Prelude SIEM extends Prelude OSS to include an ergonomic interface and various security capabilities.
It lets you continuously monitor your security posture for possible intrusion attempts and quickly analyze the cause of an alert.
You can employ Prelude SIEM to correlate, search, investigate, and compare information to identify subtle threats and maintain the integrity of evidence.
The tool lets you design and publish various formats of functional or technical reports.
Features
- Log Collection and Analysis: Prelude can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Real-Time Monitoring: Prelude can monitor system activity in real time and provide immediate notifications of any suspicious activity.
- Threat Detection and Response: Prelude uses advanced correlation rules and machine learning algorithms to detect potential security threats in real time. It can provide alerts and notifications when potential threats are identified.
- Compliance Management: Prelude can help organizations comply with industry standards and regulations such as PCI DSS, HIPAA, and GDPR. It provides pre-built compliance reports, dashboards, automated log retention, and audit capabilities.
- Customizable Rules: Prelude provides a set of pre-built rules for detecting common security threats, but also allows organizations to create their own custom rules based on their specific security needs.
- Open Source: Prelude is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
- Scalability: Prelude is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
- Visualization: Prelude provides a range of visualization tools, including dashboards and graphs, to help organizations monitor their security posture and respond to security incidents.
- Integration: Prelude can integrate with a wide range of other security tools, such as vulnerability scanners, firewalls, and intrusion prevention systems.
12. Security Onion
Deployment model: on-premise
Security Onion is a Linux distribution for enterprise security monitoring (ESM) and intrusion detection.
It offers network-based and host-based intrusion detection systems (IDS) and full packet capture (FPC), supporting various enterprise security monitoring and threat-hunting responsibilities.
Here are key features:
- Support for network-based intrusion detection systems (NIDS)—Security Onion collects network events from various tools, such as Suricata and Zeek, to provide complete coverage of the enterprise network.
- Support for host-based intrusion detection system (HIDS)—Security Onion supports host-based event collection agents, such as Wazuh, Osquery, and Beats.
- Static analysis (PCAP Import)—you can use Security Onion to import PCAP files for quick static analysis and case studies.
Features
- Log Collection and Analysis: Security Onion can collect and analyze logs from a wide range of sources, including servers, network devices, and applications. It can normalize and enrich the data to provide context and make it easier to search and analyze.
- Real-Time Monitoring: Security Onion can monitor system activity in real time and provide immediate notifications of any suspicious activity.
- Threat Detection and Response: Security Onion uses advanced correlation rules and machine learning algorithms to detect potential security threats in real time. It can provide alerts and notifications when potential threats are identified.
- Network Security Monitoring: Security Onion provides powerful network security monitoring capabilities, including full packet capture, deep packet inspection, and network flow analysis.
- Intrusion Detection: Security Onion includes several intrusion detection systems (IDS), including Snort, Suricata, and Bro. It can detect and alert on a wide range of network-based attacks.
- File Integrity Monitoring: Security Onion includes file integrity monitoring (FIM) capabilities that can detect and alert on changes to critical system files.
- Incident Response: Security Onion provides a range of incident response capabilities, including network forensics, memory analysis, and malware analysis.
- Visualization: Security Onion provides a range of visualization tools, including dashboards and graphs, to help organizations monitor their security posture and respond to security incidents.
- Open Source: Security Onion is an open-source tool that allows organizations to customize and extend the tool to meet their specific security needs.
- Scalability: Security Onion is designed to be scalable and can be used in a variety of environments, including on-premises, cloud, and hybrid. It can handle large amounts of security telemetry data and can be customized to meet the needs of organizations of all sizes.
13. Suricata

Deployment model: on-premise
Suricata is an open-source engine for high-performance network IDS, IPS, and network security monitoring.
The Open Information Security Foundation (OISF), a non-profit organization, owns it. Suricata can store TLS certificates, log HTTP request logs, and extract files from flows and store them on disks.
Suricata uses automatic protocol detection for protocols like HTTP on all ports to apply the proper detection.
It maintains integrations in JSON and YAML to support databases like Splunk and Elasticsearch and supports multithreading natively.
Features
- Multi-threaded Packet Processing: Suricata is designed to be highly performant, with multi-threaded packet processing capabilities that can process high volumes of network traffic in real time.
- Protocol Parsing: Suricata can parse and analyze a wide range of network protocols, including HTTP, SMTP, DNS, SSH, and SSL/TLS.
- Signature-Based Detection: Suricata uses signature-based detection to identify known threats and vulnerabilities based on patterns and signatures.
- Anomaly-Based Detection: Suricata can also use anomaly-based detection to identify potential threats based on deviations from expected network behavior.
- Flow Analysis: Suricata can analyze network flows to identify and alert suspicious network activity, including network scans and port scans.
- File Extraction and Analysis: Suricata can extract and analyze files in real time, including malware and other malicious files.
- TLS/SSL Decryption: Suricata can decrypt SSL/TLS traffic to analyze and detect threats that may be hidden in encrypted traffic.
- Open Source: Suricata is an open-source tool that provides organizations with the ability to customize and extend the tool to meet their specific security needs.
- Community Support: Suricata has a large and active community of users and developers who contribute to its development and provide support to other users.
Conclusion
The Best SIEM Tools List help in selecting the right product for detecting and patching the vulnerabilities in a proactive way.
With automated scanning options, you can generate weekly incident analysis reports and compare the results to gain more insight.
While many of these SIEMs are not as fully featured as commercial solutions, they provide more than enough functionality for small-to-medium organizations building their first SOC.
Above mentioned Best SIEM Tools List scanning tools are tested by our expert and listed here based on their performance.


-1.webp?w=218&resize=218,150&ssl=1)



