Brute force attacks have been one of the most common attack types. In Q1 2022, brute force made up 51% of all attacks! These attacks often pave the way for other types of threats and have devastating consequences for the organization.
Brute force on APIs is a bigger problem since APIs programmatically expose data, functionalities, and business logic. You need to act urgently to stop these attacks and keep your digital assets secure from attackers.
Want to know how? Keep reading to find out more about brute force attacks and ways to protect your APIs, apps, and websites against them.
Table of Contents
What is a Brute Force Attack?
Brute Force in APIs
Brute Force vs. Other Cracking Techniques
Types of Brute Force Attacks
How Do Brute Force Attacks Work?
Real-life Examples
What Factors Lead to Brute Force Attacks?
Who Are Common Targets for Brute Force Attacks?
What Makes Brute Force API Attacks Dangerous?
Protecting Against Brute Force API Attacks
Brute Force Attack Detection
Access violations
Strong Password Policies & Multifactor Authentication
Robust Access Control and Authorization Policies
Lockout Policies
Progressive Delays
Implement CAPTCHA Challenges Intelligently
Use Hashing to Secure Passwords
Bot Mitigation
Conclusion
What is a Brute Force Attack?
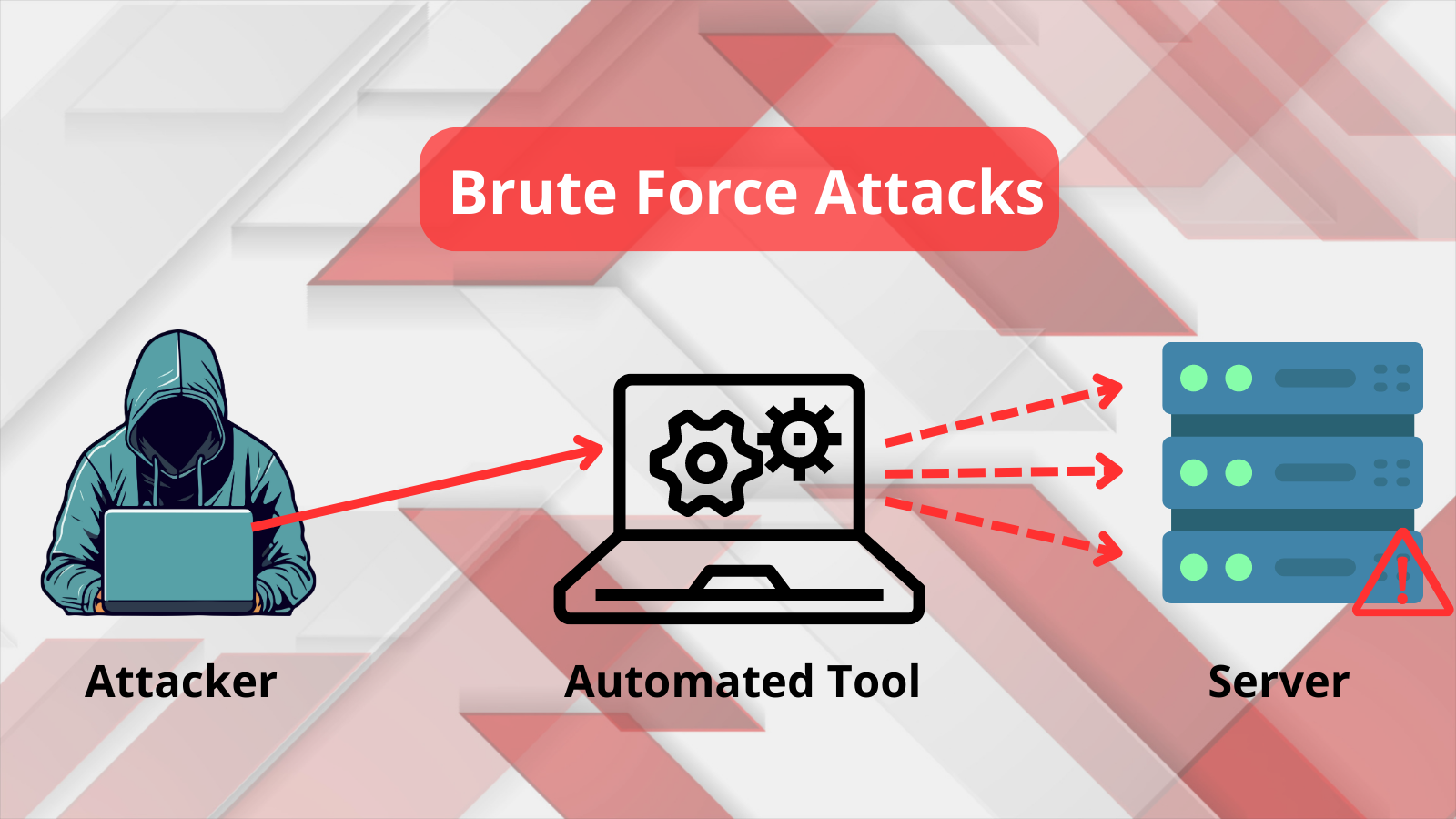
Brute force attacks are common, simple, and easy-to-orchestrate credential cracking/ password guessing attack types. In these attacks, the threat actor uses trial and error to decode passwords, login credentials, API keys, SSH logins, encryption keys, hidden web pages, and content. Thereon, they gain unauthorized access to apps, APIs, accounts, systems, and networks.
Attackers keep guessing usernames and passwords till they find valid combinations. They systematically try all possible combinations of letters, numbers, and symbols until they crack the credentials. Attackers may use manual or automated methods to inject username passwords and find the right credentials.
Brute Force in APIs
Brute force in APIs is an attack where the threat actors leverage tools to continuously send requests to APIs to guess correct combinations of credentials. The end goal may be anything from stealing an account by brute forcing API authentication forms to exfiltrate sensitive data by brute forcing logins.
Brute Force vs. Other Cracking Techniques
Brute force attacks don’t use an intellectual strategy to crack credentials; they use a simple trial-and-error method instead. They try exhaustively to break credentials by trying various combinations of characters till they find a combination that allows them to enter. This is the main difference between brute force and other stuffing & cracking methods.
In credential stuffing attacks, attackers throw bona fide login credentials to fool the API/ app into believing they are legitimate users. To this end, they use stolen credentials and keys.
In brute force attacks, attackers repeatedly attempt different character combinations until they gain access to the API or app.
Types of Brute Force Attacks
- Simple brute force attacks where attackers use a simple, systematic approach to guess and crack credentials without relying on intellectual strategy or logic. Automated tools and scripts are typically used to automate guessing credentials.
- Dictionary attacks are where attackers use a common database of words, strings, and phrases – a dictionary. They start with a word/ phrase from the dictionary and try combinations of letters and characters to determine the login credentials.
- Hybrid brute force attacks are where attackers combine aspects of simple and dictionary attacks. They use external logic to determine password variations that may have a higher probability of success and then amend those to try various combinations.
- Rainbow table attacks where attackers use a rainbow table – a precomputed table/ dictionary of plaintext passwords and hash functions corresponding to them. Using the rainbow table, they try to reverse cryptographic hash functions.
- Reverse brute force attacks where attackers use common/known passwords or collections of passwords against possible usernames/ account numbers by trying different combinations.
- Password spraying attacks where attackers take commonly used passwords like admin or 123456 and use them across different accounts instead of trying different password combinations. This is used in cases where account lockout policies are in place, and attackers have only limited attempts to crack credentials.
- Botnet brute force attacks where attackers leverage powerful bots to brute force APIs, apps, and networks. One of the biggest drawbacks of brute force for attackers is that it takes days, even months, to crack credentials, especially more complex ones. With additional security measures like rate limiting and account lockout policies, the challenges are even bigger. But botnets help overcome these challenges. They provide high computing power to attackers and help them evade traditional defenses while infusing speed and efficiency into the process.
How Do Brute Force Attacks Work?
Traditional brute force attacks typically use exhaustive manual effort to crack credentials. But given the security measures at play and the time it takes to crack a single complex password, attackers today leverage automated tools, scripts, and powerful botnets to brute force APIs, apps, and networks.
These tools and bots can send voluminous server requests and make hundreds of thousands of login attempts per hour. They can guess and find combinations that work in minutes rather than weeks or months.
There are 3 broad steps in brute force attacks that use automated tools and bots.
- Attackers identify the target URLs of the APIs, apps, or sites they want to attack and preconfigure parameter values in the brute force tool.
- They run the brute force processes using the tool/ bot, which attempts to identify all valid credentials.
- Upon identifying successful login credentials, attackers log in and do their bidding.
Here are some of the common tools attackers use for brute forcing:
- THC-Hydra runs a large number of password combinations using simple or dictionary-based methods to crack network password protocols.
- Aircrack-ng uses a dictionary of widely used passwords to breach wireless networks.
- John the Ripper is a tool that exhaustively runs possible combinations using a dictionary.
- Hashcat is the fastest CPU-based cracking tool that runs simple brute force, rule-based, and hybrid attacks.
- Ncrack helps crack network authentication and supports various attack types.
- RainbowCrack is one of the fastest cracking tools that leverage rainbow tables.
Real-life Examples
The Canadian Revenue Agency faced a brute force attack in 2020, compromising 11,000 accounts of CRA and other government-related services. Attackers used previously stolen credentials to brute force the agency.
In 2018, Magneto, an e-commerce platform, was a victim of a brute force attack that compromised its admin panels. No less than 1,000 account credentials were exposed on the dark web.
In 2018, the Northern Ireland Parliament was brute forced, exposing the accounts of some of its members. Hackers are known to have used several combinations to crack passwords and access the mailboxes of these members.
TaoBao, an Alibaba e-commerce site, was brute forced in 2016, compromising 21 million accounts (1/5th of all TaoBao accounts). Attackers used a database of 99 million usernames and passwords to orchestrate this brute-force attack.
What Factors Lead to Brute Force Attacks?
One of the top causes of brute force attacks is poor password practices.
Users, including admin accounts, use simple or generic passwords like 123456, abdce, 111111, or admin. These are easy to crack.
Even when users use stronger passwords, they reuse them across accounts and platforms. So, if their credentials were stolen from one account, all their other accounts using the same credentials are at risk of exposure.
Organizations use predictable taxonomies for the login credentials, creating patterns that are easy to detect. For instance, the employee’s initial and last names followed by the company name for login IDs are commonly used.
Many organizations continue to store credentials, API keys, encryption keys, and passwords in plaintext or poorly encrypted databases. So, attackers can exfiltrate these databases and use them for brute forcing APIs and apps.
Organizations continue to rely on passwords or keys as their only authentication mechanism. Even when organizations use MFA (multifactor authentication), they are still at risk if they don’t have proper authorization and role-based access control measures.
Furthermore, organizations often overlook the importance of implementing multi-layered security measures such as account lockout and rate limiting to prevent brute force attacks.
Who Are Common Targets for Brute Force Attacks?
If your website/ API/ app/ system requires user authentication, it will be targeted by threat actors. Brute force attacks are much easier to orchestrate than other attacks since attackers don’t have to scan for and develop ways to exploit vulnerabilities.
However, e-commerce APIs, apps, and sites are the most common targets of these attacks. This is because they process payments and have access to large volumes of sensitive customer data such as PII, banking information, credit card details, and so on. Suppose an attacker gains access to an e-commerce API or site. In that case, they can easily perform data breaches, financial theft, identity theft, sell user information on the dark web, and so on. This causes distrust among users and affects the reputation of the organization.
What Makes Brute Force API Attacks Dangerous?
Impact
The impact of brute force on APIs is severe and damaging. Because APIs expose data and functionalities by their very nature, attackers brute force them to discover login credentials and API keys to access user accounts and the app to find more vulnerabilities.
By brute forcing APIs, attackers can also cause downtimes and crashes for other users. They could lock out legitimate users by brute forcing APIs with a lockout mechanism for failed logins.
Successful login attempts enable attackers to exfiltrate user information, keys, and so on that they can sell on the dark web. They could also spread malware, engage in account takeover, and perform other attacks.
Other Reasons Why They Are Dangerous
- They are easy and simple to orchestrate, especially with the easy availability of automation tools and bots for hire.
- The weak password problem still exists.
- Even if attackers don’t find or can’t use other vulnerabilities, brute force attacks work.
Protecting Against Brute Force API Attacks
Brute Force Attack Detection
Before knowing how to prevent them, you need to understand how to detect brute-force attacks.
Firstly, you need to continuously monitor incoming traffic and user behavior using an API-specific, fully managed, intuitive security solution. AppTrana API protection uses behavioral and pattern analysis to identify anomalous behaviors and patterns. Some examples :
- Serious failed login attempts
- Unusual patterns of failed logins
- Unusual user behavior after successful login
- One successful login followed numerous failed attempts
- Successful login coming in from an unusual IP address
- Successful login into different accounts from the same IP address
- Unusual network activity
- Unusually high number of login requests to APIs
Access violations
The security solution must provide real-time alerts and triggers when unusual activities happen. Only then you can take instant action to stop attacks.
Your API-specific security solution must include automated scanning tools equipped with AI-ML and threat intelligence to find authentication flaws that allow brute-force attacks proactively.
You must use manual pen-testing to find authentication flaws and other weaknesses that enable brute forcing of your APIs. To ensure a comprehensive assessment, following an API penetration testing checklist is essential, which will guide you through the systematic evaluation of your API’s security measures.
Strong Password Policies & Multifactor Authentication
This is the most important way to prevent brute force API and other attacks.
- Create complex passwords containing a combination of alphanumeric and special characters.
- Reject generic and weak passwords for enhanced security.
- Avoid common patterns when crafting usernames and passwords.
- Ensure password expiration at regular intervals and disallow the reuse of prior passwords.
- Educate users on the significance of crafting distinct passwords for individual accounts or platforms.
- Explore the adoption of a password manager or embrace passwordless authentication.
- Prevent storing passwords, keys, and credentials in plaintext.
- Implement 2FA or MFA as mandatory measures for APIs and websites, particularly for those granting access to sensitive data and features. These steps provide supplementary safeguards for your APIs and accounts.
Robust Access Control and Authorization Policies
Even when a successful login happens, the attacker shouldn’t be able to access too much sensitive information. This is why role-based access control and strong authorization policies are necessary. Also, ensure that unused accounts, especially high-permission accounts, are closed.
Lockout Policies
The account should automatically be locked if the number of failed attempts exceeds the preset limit. Only the administrator should be able to unlock the account after verification from the user.
Remember, there is a possibility that competitors brute force you to lock out your legitimate users. By doing so, they can create mistrust and a loss of reputation for your organization. This is why you need to prohibit multiple login attempts from the same IP address for different accounts.
Progressive Delays
You can also lockout accounts temporarily after failed login attempts and implement progressive delays between each failed login. This slows down brute force attacks.
Implement CAPTCHA Challenges Intelligently
Brute force tools and bots cannot perform CAPTCHA challenges. So, you can create hurdles for attackers by implementing these challenges. Your security solution must implement these challenges intelligently based on real-time insights.
Use Hashing to Secure Passwords
Randomized password hashing is a vital rest API brute force protection measure. Password hashing protects the systems even when it is compromised owing to successful attacks.
Bot Mitigation
Since modern-day brute force attacks widely leverage bots and automated tools, you must use a security solution that offers intelligent, fully managed bot mitigation capabilities.
Conclusion
With an API-specific, fully managed, comprehensive security solution like AppTrana, you can proactively hunt down brute force threats and prevent attackers from brute forcing your APIs.