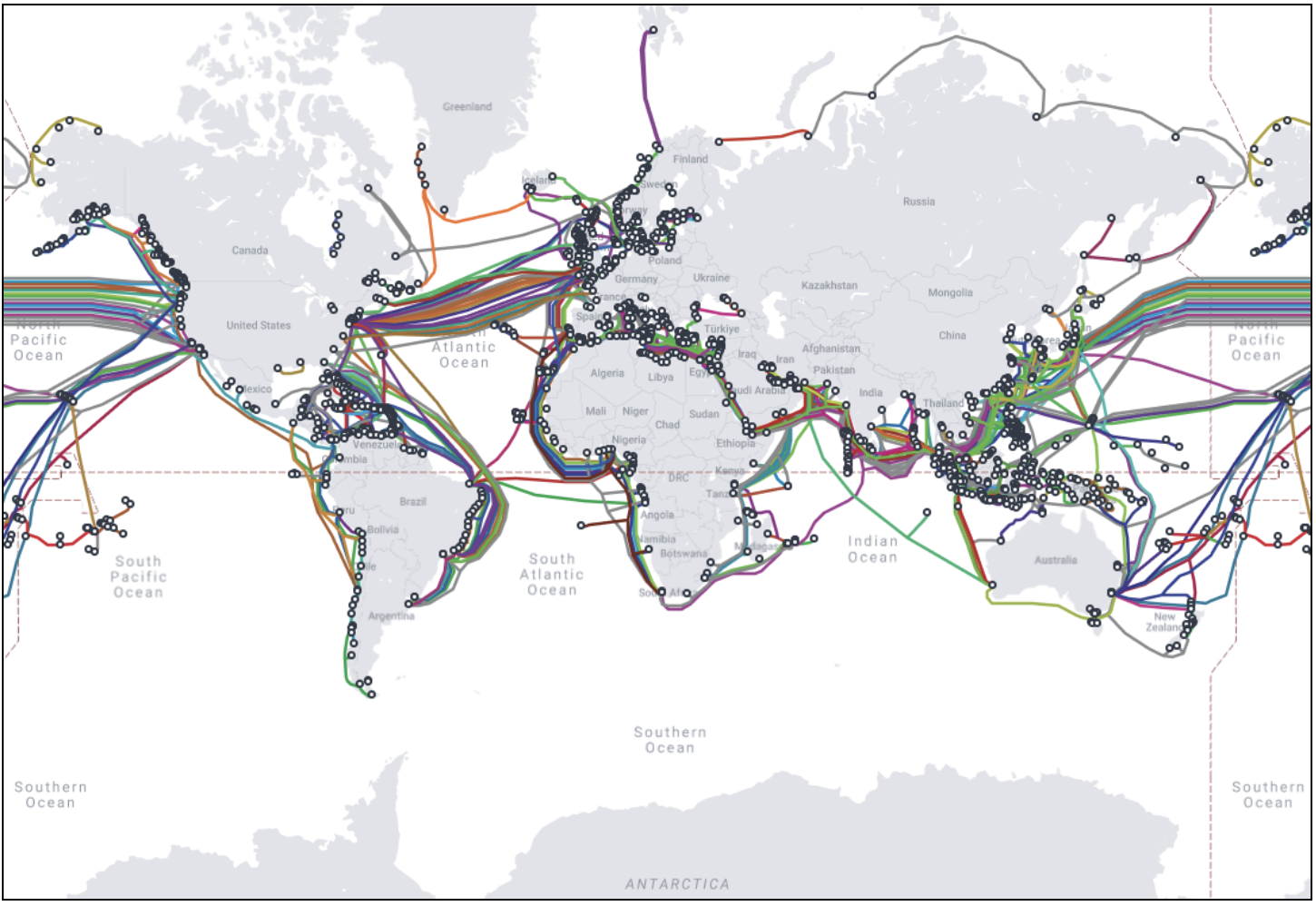
Submarine cables installed on the ocean floor facilitate the transmission of data and voice between land-based stations.
International communication has relied on submarine cables since the first one was laid across the English Channel in 1850. This cable was used to transmit telegraph messages between England and France.
Using fiber-optic cables for telecommunications has proven to be a superior option compared to satellite-based alternatives. These cables are not only faster and more reliable but also more cost-effective.
They consist of thin strands of glass that transmit data as light pulses encased in layers of plastic, steel wires, copper sheathing, and polyethylene insulation.
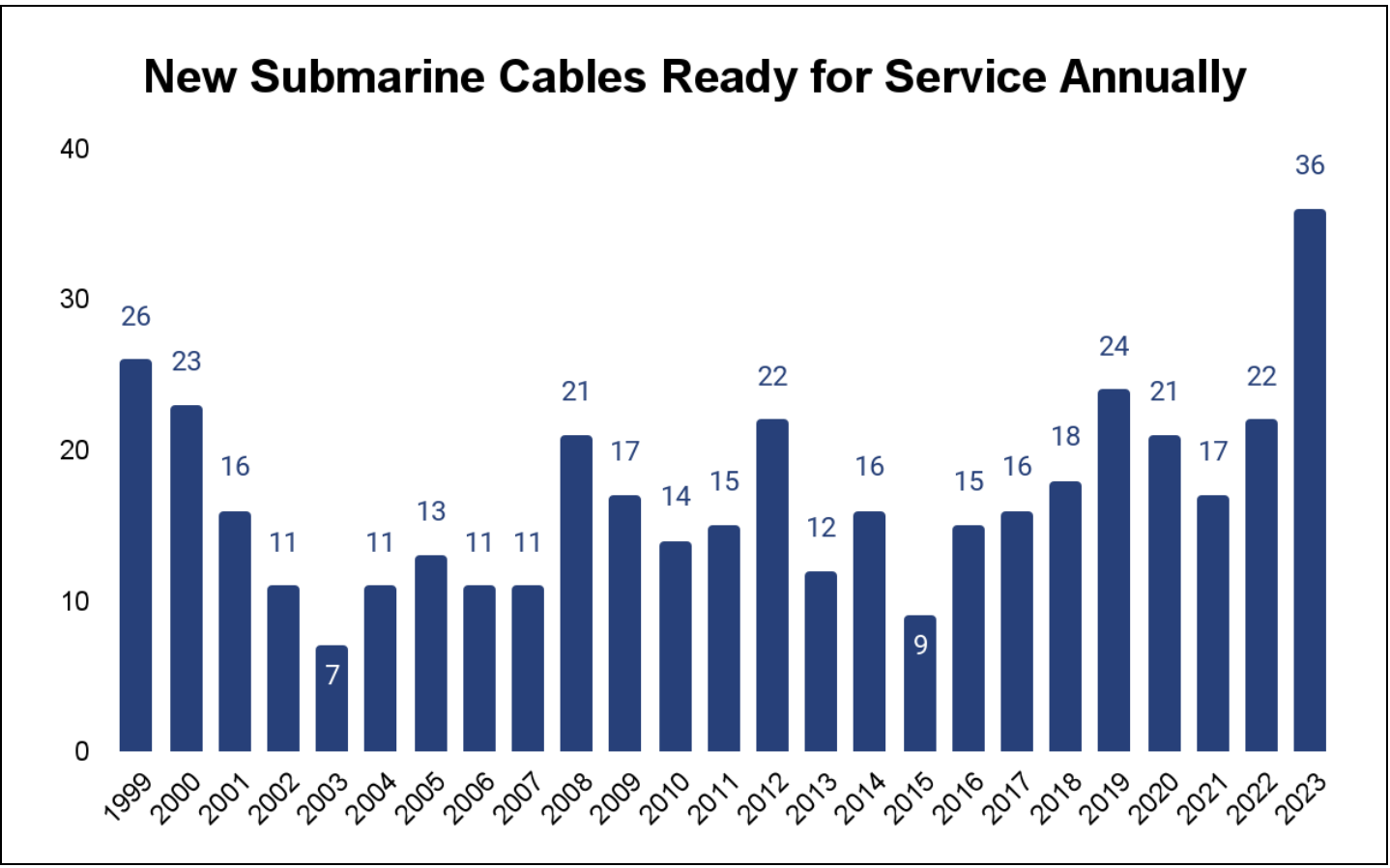
Reports indicate that there will be a significant rise in traffic, with a projected compound annual growth rate of approximately 28% from 2022 to 2030, resulting in a monthly data consumption of 603.5 million terabytes.
Expansion Poses Cyber Security Risks
A report by Recordfuture states that Chinese state-owned enterprises have been striving for a larger share in the global submarine cable network since the beginning of the 21st century.
China is currently increasing its ownership and operation of cables around the globe, which gives them more control over the deployment of submarine cables in specific locations.
Every year, there are more than 100 submarine cable faults where the cables get damaged or severed completely, disrupting data transmission.
Most of these damages are physical and tend to happen by accident, frequently caused by fishing boats.
Given their resources and motives, state-sponsored organizations pose the greatest risk of deliberate espionage and sabotage.
To optimize the performance of submarine cables and improve their operations, owners are utilizing network management tools to manage their infrastructure efficiently.
Network management tools are connected to the internet, making them vulnerable to targeted attacks from state-sponsored adversaries, ransomware groups, hacktivists, and other cyber threat actors.
In April 2022, an attempted cyberattack against a submarine cable operating system in Hawaii was foiled by federal authorities. The attack was made possible by a breach of a third party’s credentials.
According to a prediction by Record Future, there is a significant likelihood of espionage activities aimed at the entire submarine cable system. This encompasses the landing station infrastructure, submarine cables, third-party providers, and the hardware and software that link all these elements.
It’s important to stay alert and take necessary precautions to prevent any unauthorized access or data breaches.
Submarine cable networks and operating systems may potentially be at risk from non-state actors like hacktivists and ransomware gangs.
“AI-based email security measures Protect your business From Email Threats!” – .



