SolarWinds released a security advisory for addressing a Directory Traversal vulnerability which allows a threat actor to read sensitive files on the host machine.
This vulnerability existed in the SolarWinds Serv-U File Transfer solution and was assigned with CVE-2024-28995 – 8.6 (High).
This vulnerability affected multiple SolarWinds Serv-products in both Windows and Linux platforms.
However, it was fixed in the latest version, SolarWinds Serv-U 15.4.2 HF 2. The company also recommends that users upgrade their products to the latest version.
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot
Technical Analysis – CVE-2024-28995
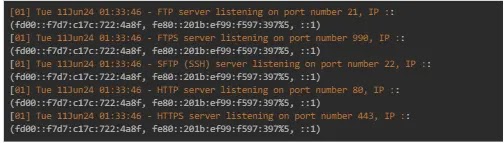
According to the reports shared with Cyber Security News, this vulnerability affected Server-U FTP server 15.4, Serv-U Gateway 15.4 and Serv-U MFT Server 15.4.
The Serv-U is a C++-written application that contains the majority of the code in the Serv-U.dll binary.
On analyzing this binary further, it was discovered that there was a modified function sub_18016DC30.
This modified version of this function processes a file path with added checks. The check was written in such a way that it checks particularly for the double dot path segment (\..\) and if found, it is sanitized.
Further investigations concluded that most of this function’s use cases contain two HTTP request parameters, InternalDir and InternalFile, both of which call the vulnerable function.

However, when providing a directory traversal payload to these parameters on a vulnerable version of Serv-U, the application processed the payload and triggered the directory traversal vulnerability.
This vulnerability can also be modified to reach an arbitrary file on the target server that could reveal sensitive information.
As an added fact, if the Serv-U application is installed on a Windows machine, the system data will be stored in the following path C:\ProgramData\RhinoSoft\Serv-U\.
Further, Serv-U-StartupLog.txt on the system data folder contains the application logging information emitted during application startup and will also include the target Serv-U server’s version number.
On a Linux platform, this vulnerability can be triggered to read.
.webp)
.webp)
Users of SolarWinds Serv-U are recommended to upgrade to the latest version or apply the 15.4.2 Hotfix 2 to remediate this vulnerability.
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free



