The ‘Decoy Dog’ malware toolkit, aimed at enterprises, was uncovered recently by the security analysts at Infoblox by analyzing 70 billion DNS records and traffic that differs from typical online behavior.
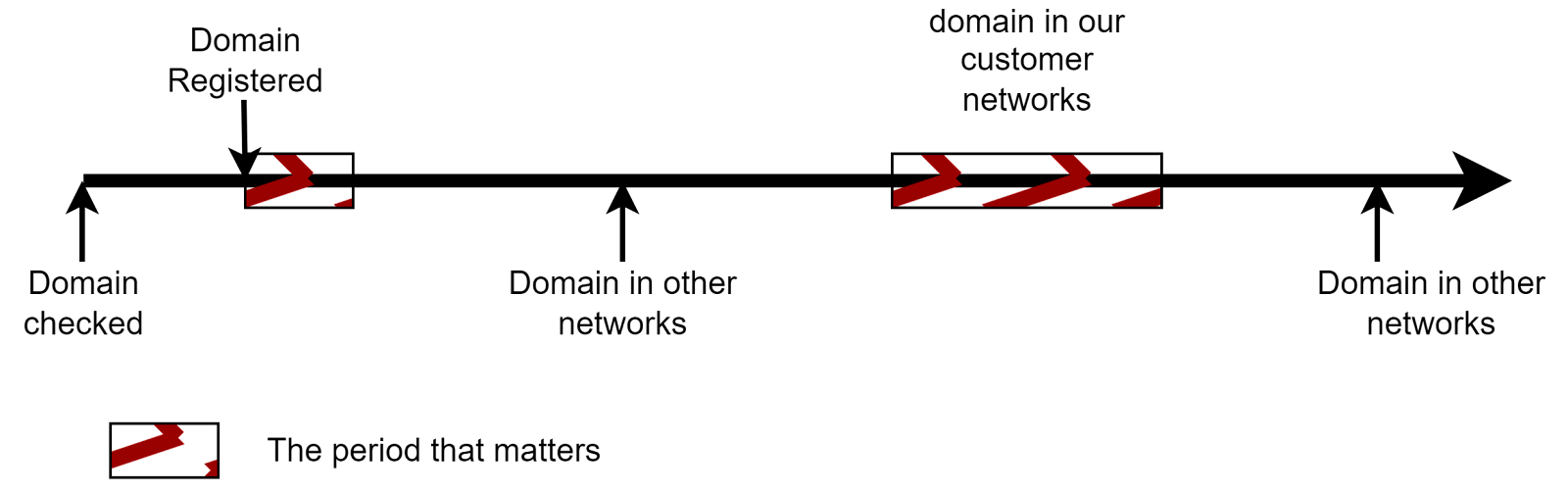
Decoy Dog was discovered in early April 2023, and by using domain aging and DNS query dribbling tactics, the Decoy Dog malware assists threat actors in avoiding traditional detection methods.
This strategy enables them to build a positive reputation with security vendors before transitioning to supporting cybercrime activities.
Decoy Dog has an exceptionally rare and distinct DNS fingerprint compared to the 370 million active domains on the internet, facilitating its identification and tracking.
Technical Analysis
Numerous C2 domains related to the operation were identified after the inquiry into Decoy Dog’s infrastructure. The majority of these server communications emerged from Russian-based hosts.
Apart from this, a RAT utilized by the Decoy Dog toolkit has been identified while analyzing the DNS tunnels on these domains, and the RAT is dubbed “Pupy RAT.”
State-sponsored threat actors favor Pupy RAT due to its modularity, open-source nature, and stealth capabilities (fileless execution), which enable them to blend in with other users and support encrypted C2 communications.
Here below, we have mentioned the domains that were flagged for suspicious activity in early April 2023:-
- cbox4[.]ignorelist[.]com
- claudfront[.]net
- hsdps[.]cc
- ads-tm-glb[.]click
- atlas-upd[.]com
- allowlisted[.]net
In all major operating systems, the Pupy RAT project supports the payloads, and here below, we have mentioned the OS platforms:-
- Windows
- macOS
- Linux
- Android
Here below, we have mentioned the capabilities of Pupy RAT:-
- Enables execution of commands remotely
- Elevate privileges
- Steal credentials
- Spread laterally through a network
Less experienced actors do not commonly use Pupy RAT since setting up the appropriate DNS server configuration for C2 communications is complicated and unsuitable for less experienced actors.
The DNS signature spanning multiple parts provided a high level of certainty that the correlated domains were part of the Decoy Dog toolkit, which distinctly utilizes Pupy RAT on non-consumer devices, such as those found in large enterprises or organizations.
Characteristics of Decoy Dog’s Toolkit
Here below, we have mentioned the characteristics of Decoy Dog’s toolkit:-
- Pupy RAT
- Unique DNS Signature
- DNS Beaconing
- Outlier Behavior
- Shared Hosting
- Registration Similarities
- Enterprise Focus
Analysts also detected a unique DNS beaconing pattern on all Decoy Dog domains that conforms to the infrequent but regular generation of DNS requests at set intervals.

Decoy Dog has operated secretly since April 2022, unnoticed for over a year despite analytics detecting unusual activity in its toolkit domains.
Detecting anomalous activity in the massiveness of the internet is made possible by using large-scale data analytics, and the discovery of Decoy Dog is a perfect example.
Building Your Malware Defense Strategy – Download Free E-Book



