Ransomware attack is quite common nowadays since Malicious software spreading everywhere through various mediums. The cybercriminals that use it are looking to do one thing, extort your money. Not unlike the movies, it usually starts with an ominous ransom note demanding money.
This usually appears in the form of a notification that pops up on your screen, that says “your data has been encrypted, pay $$$$, to get the decryption key”.
Before you run away terrified and worse revert to pen and paper, here’s the good news.
There are ways to prevent ransomware and protect yourself. In this article you will find straight-forward expert tips, so you never become a victim of Ransomware Attack.
#1: How does Ransomware work?
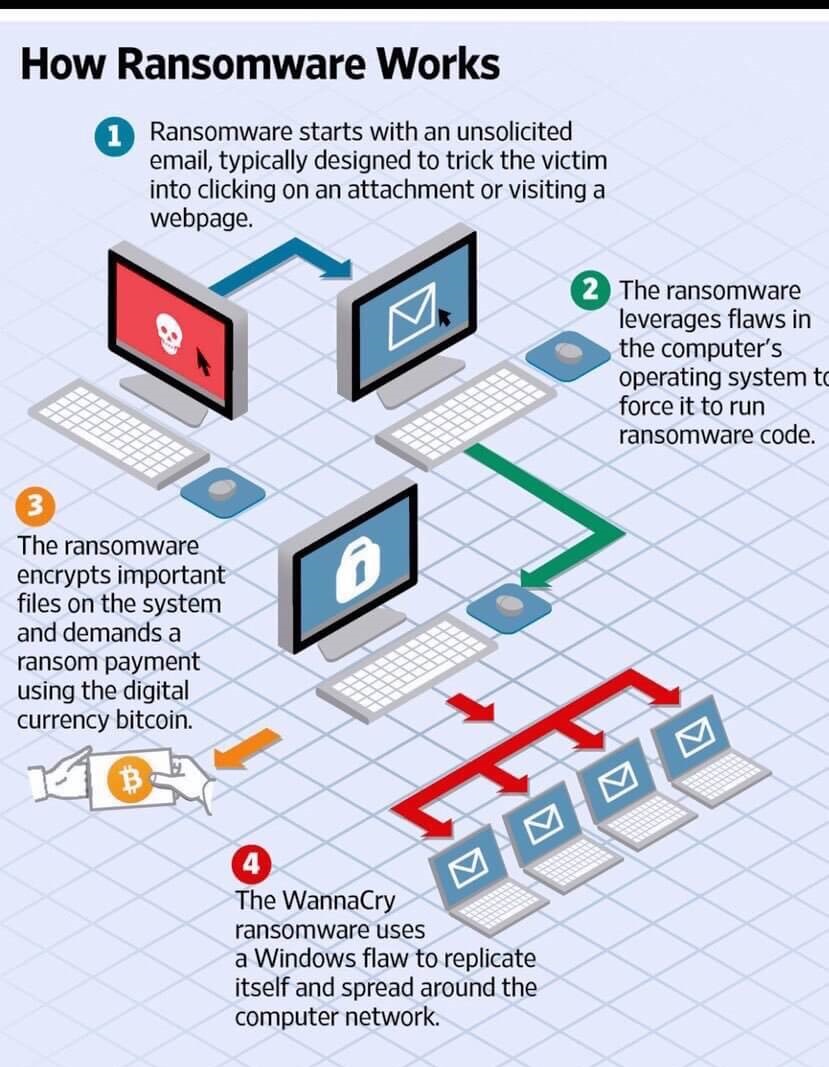
As mentioned it begins with an ominous note BUT it needs to be activated to begin the process. This is usually done through a link or email. The “lifecycle” of Ransomware Attack looks like this:
- Malicious link or email
- File types are encrypted
- Notification
- Ransom gets paid
- Full access is returned
In case this sounds rare, in 2019 alone experts are projecting a whopping $20 billion in damages connected to Ransomware AttackRansomware Attack. That’s a 195% increase since 2018.
The biggest targets tend to be government, healthcare, or school systems. As you can see any of those can be devastating.
#2: Ransomware Protection
When it comes to ransomware protection, the best solution is prevention.Here are just a handful of do’s and don’ts so you can prevent a ransomware attack:
DO NOT provide personal info when answering an email, unsolicited phone call, text, or IM.
DO use content scanning on your mail server. All inbound emails should be scanned for any known threats and block attachments.
DO make sure everything is up-to-date with patches so vulnerable software can’t be tampered.
DO NOT pay the ransom. AS per the FBI, not paying will hopefully discourage cybercriminals from attacking you or others.
DO educate yourself about different types of Ransomware Attack, to stay protected.
DO employ a layered approach to your security.

#3: Ransomware Attack Detected: Now What
As mentioned prevention is the best way to have ransomware protection. Not all protection is made equal, however. Ransomware Attack typically follows a 10-step process that looks like this:
- Threat is detected – attacker has generated a malicious link
- Skates by filters
- Enters email browser or app
- Link activates
- Antivirus bypassed
- Malware is released
- Attacks your remote server and network connection
- Dark web exfiltration
- Infection
- Attacked
Notice that there were multiple “protections” in place: filters and antivirus’ all didn’t do the job. Employing a multi-layered system, cybersecurity companies such as Blackfog can actually detect and remove an attack in real-time.
They employ multiple points of defense from profiling, suspicious address, spyware, malvertising, Facebook, Dark Web, crypto mining, application gateway, malware, forensics, geofencing, and PowerShell, Phishing.
In other words, it’s the difference between having a couple of locks on your door to having every point of access to your home secured, protected, and watched 24/7.

Take Away
Unfortunately, when it comes to Ransomware Attack, it probably will be around for a long time.
This easy and malicious way of robbing individuals and company’s can cost billions of dollars not to mention the privacy and safety implications.
There is hope in ransomware prevention through educating yourself on what to look out for and what to do if you do get attacked.
True ransomware protection happens with a multi-layered defense system, that seals up all the spots these malicious intruders would break-in. Don’t be afraid, be protected.



